 The course gives an introduction to:
The course gives an introduction to:
This course was taught by Erik Poll and Peter Schwabe.
 The course gives an introduction to:
The course gives an introduction to:
| Jan 30, lecture 1 | Intro (slides) and C-data types and their representation (slides) |
| Feb 1, Lab session 1 |
The Linux command line, gcc, and make. [linux-cheat-sheet]
[alternative cheat sheet by Felix Stegerman]
Assignment 1 Makefile main.c hello.c addvector.c addvector.h |
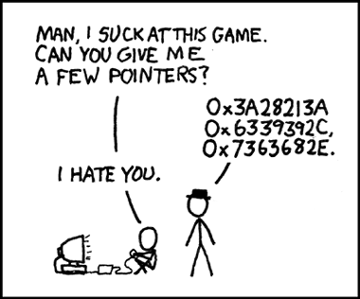
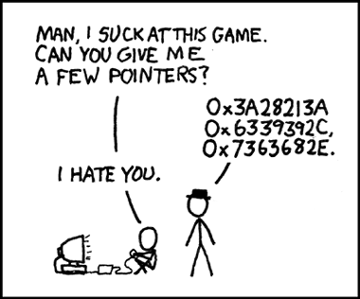
| Feb 6, lecture 2 | Alignment, arrays and pointers (slides) You can read Section 9.1 of your 'Program Solving with C++' book (used in the Imperative Programming course) for another explanation of pointers. Or, a bit childish but great for revision: Binky pointer fun movie by Nick Parlante Code examples demo-ed in lecture 2. Compile where_is_data_allocated.c with or without the option -O2 to get gcc to re-align data differently. |
| Feb 8, Lab session 3 | Memory layout and pointer arithmetic. Assignment 2 |
| Feb 13, lecture 3 | Pointers continued(slides) and
memory management: the stack(slides)
Code samples demo-ed in the lecture
|
| Feb 15, Lab session 4 | Playing around on the stack and the heap. Assignment 3 |
| Feb 20, lecture 4 | The heap, and more stack and heap issues (slides):
overflow, memory leaks, and problems with malloc & free
Code samples demo-ed in the lecture
|
| Feb 22, Lab session 5 |
Memory leaks and attacks. Introduction to gdb. Assignment 4 pwd-normal, pwd-hard You might find this GDB Quick Reference helpful. |
| March 6, lecture 5 | Format string attacks and buffer overflows (slides) Read the tutorial on buffer overflows by Herbert Bos and lecture notes on format strings by Wenliang Du. A bufferflow overflow attack is similar to phreaking attack on the phone system (video): In a buffer overflow attack, malicious input tricks the CPU into doing something; in a phone phreaking attack, malicious input - by whistling! - tricks the phone system into doing something, namely dialing numbers for free. |
| March 8, Lab session 6 |
Assignment 5.
If the server hackme.cs.ru.nl should not be reachable, email Pol van Aubel.
Additional tips for the final challenge to hack the server: When using format strings to analyse the stack layout, using strings with lots of %p's is the most convenient, as %p will print stack data as (in this case 64 bit) pointer values. |
| March 13, lecture 6 | More attacks and some defences: Canaries, non-executable stack, ASLR (slides) |
| March 15, Lab session 7 | More work on assignment 5. |
| March 20, lecture 7 |
Root causes(slides)
Demonstration and discussion of attack on the server (from assignment 5). |
| Thursday April 6, 8:30-11:30 | exam in HG00.304 and HG00.307 voorbeeld tentamen (We don't provide a sample solution. NB unlike in some earlier years, we will not ask questions about bash scripts in the exam.) |
Parts of the course are inspired by on material from the SysSec Common Curriculum, and the course is part of the 10K Students Challenge to teach 10 thousand students the basics of software vulnerabilities and secure programming.
